On 4 March 2026, the Cyber Jihad Movement (CJM) issued a communiqué on its official Signal channel announcing its “entrance into the Iranian-American war and the Afghanistan-Pakistan war”, marking a significant inflexion point in al-Qaeda’s cyber strategy. Issued just days after the United States and Israel launched Operation “Epic Fury” and Operation “Roaring Lion” on 28 February 2026, – strikes that killed Supreme Leader Ali Khamenei and devastated critical infrastructures – the statement emerges at a moment of significant geopolitical upheaval. It reveals al-Qaeda-affiliated hackers opportunistically tapping into Iran’s extensive Islamic Revolutionary Guard Corps (IRGC)-backed cyber apparatus to gain access and operational deniability – obscuring responsibility for an attack and complicating attribution. This Insight will analyse how the CJM’s announcement represents a tactical convergence between ideologically disparate actors in cyberspace, discuss the current wartime cyber landscape in Iran, and discuss the potential role of AI. It will conclude with practical PCVE and counterterrorism cyber recommendations focused on function-based detection rather than ideology-centric attribution models.
CJM Statement and al-Qaeda’s Evolving Cyber Efforts
The CJM emerged in 2025 as a hacktivist collective conducting distributed denial-of-service (DDoS) attacks targeting US institutions and European governments. DDoS is a type of cyberattack in which multiple compromised systems simultaneously send large volumes of network traffic or service requests to a targeted server, network, or online service to exhaust its processing capacity or bandwidth. In August 2025, CJM formally pledged bay’ah (allegiance) to al-Qaeda, establishing itself as the network’s primary cyber arm. Analysts noted the group’s capability extending beyond website defacements to sustain DDoS campaigns against financial and governmental infrastructures, positioning CJM within al-Qaeda’s broader technological evolution. This development aligns with guidance from al-Qaeda’s current leader, Saif al-Adel, who has consistently urged militants to update their knowledge “according to time and technology”. In his strategic writings analysed by the Modern War Institute, al-Adel identifies drones, remotely operated systems, and cyber capabilities as force multipliers, advocating for “electronic hacks” targeting transportation and infrastructure to exploit asymmetric advantages. Al-Qaeda affiliates have demonstrated this technological adaptability through weaponised drone deployment in West Africa and AI experimentation – what security analysts term al-Qaeda’s “third phase” of operations.
The March 4th communiqué in Image 1 synthesises this strategic vision. Invoking the basmala (“In the name of Allah, the Most Gracious, the Most Merciful”), CJM calls upon “believing men and women” to join “Global Cyber Jihad” and inflict “financial loss and cyber disruptions” against American, Israeli, Pakistani, Indian, and Arab governments. Critically, the statement announces CJM will “give cyber assistance to the Mujahideen of Pakistani Taliban and the Islamic Emirate of Afghanistan” whilst joining “pro-Iranian hacker movements and groups in their fight against the United States and Israel”. This represents the first explicit declaration of cross-ideological cyber collaboration between Sunni jihadist and Shia-aligned hacker collectives.
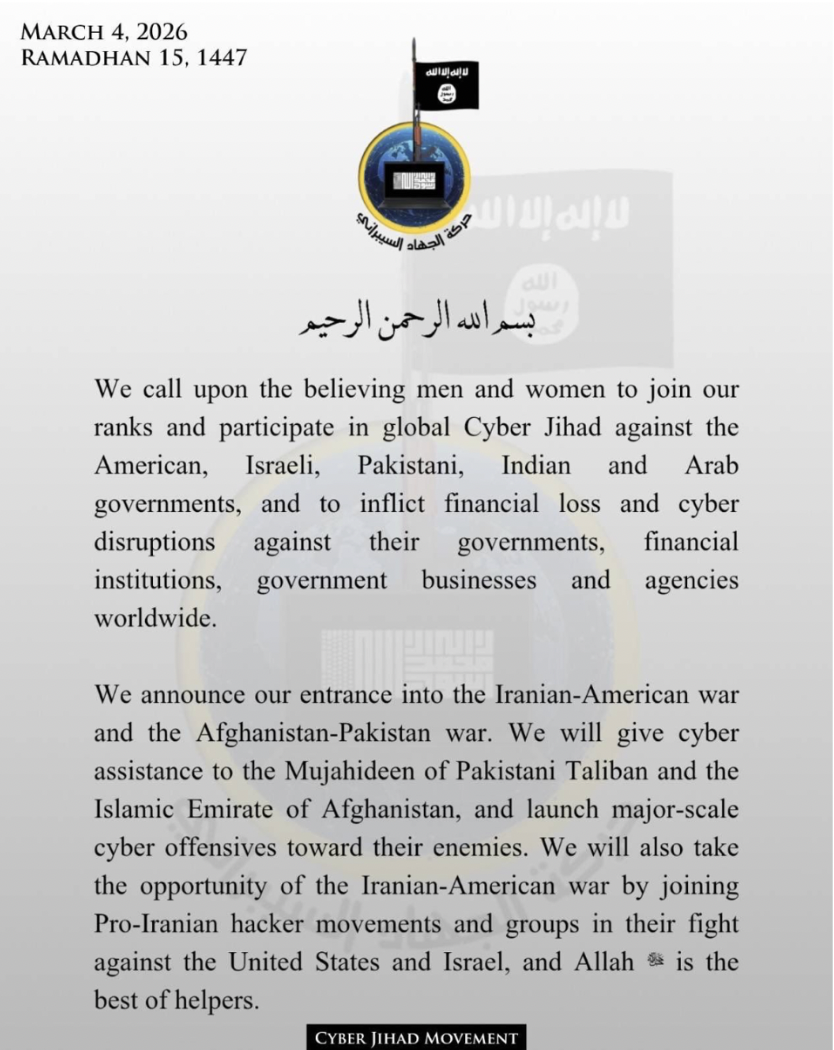
Image 1. Screenshot of the CJM communiqué dated 4 March 2026, calling upon believers worldwide to join Global Cyber Jihad against shared adversaries.
Iran’s Current Wartime Cyber Landscape
To understand why CJM views Iran’s cyber infrastructure as a viable partner for collaboration, one must examine the unprecedented scale and coordination of Iran’s ongoing cyber operations amidst the current war. Within nine hours of the strikes on February 28th, pro-Iranian hacktivist groups launched 149 DDoS attacks against 110 organisations across 16 countries. Threat intelligence documented two groups – Keymous+ and DieNet – that accounted for 70% of attack activity during the campaign’s initial days, with at least 12 different hacktivist collectives participating.
Image 2. Message on DieNet’s official group on Telegram, sent on the 3rd of March, where the group claims the targeting of Jordan’s Ministry of Finance’s website.
This surge operates within a structured command architecture. The “Electronic Operations Room”, established on 28 February 2026, functions as the primary coordination hub for Iran-aligned hacktivist operations. Research by SecurityScorecard’s STRIKE team analysed 250,000 messages from 178 active groups during the previous 12-day conflict between Israel and Iran earlier in 2025, revealing that attack timings and target selection exchanged across collectives suggested institutional IRGC orchestration rather than organic activism. Groups such as Handala Hack (linked to Iran’s Ministry of Intelligence and Security), Cyber Fattah, Fatimiyoun Cyber Team, and Islamic Cyber Resistance conducted reconnaissance, DDoS campaigns, and data-theft operations in coordination with military developments.
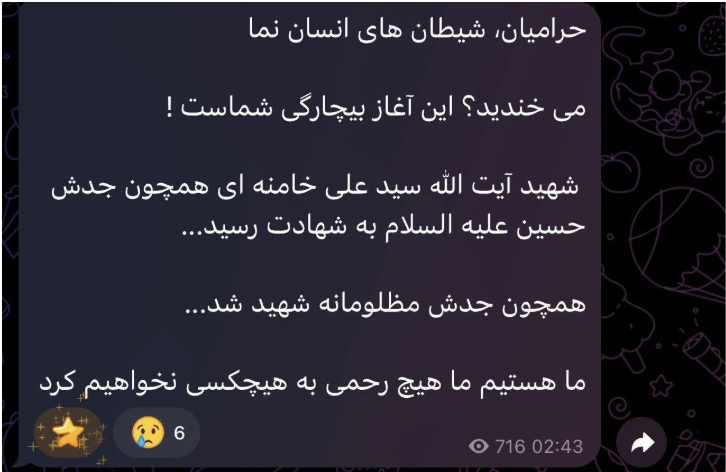
Image 3. Message on the “Cyber Fattah Team” group on Telegram, sent on the 1st of March. Translation: “Thieves, humanoid devils; Are you laughing? This is the beginning of your misery! Martyr Ayatollah Seyyed Ali Khamenei was martyred like his grandfather Hussein (peace be upon him)…Like his grandfather, he was martyred unjustly…We are here, we will show no mercy to anyone.”
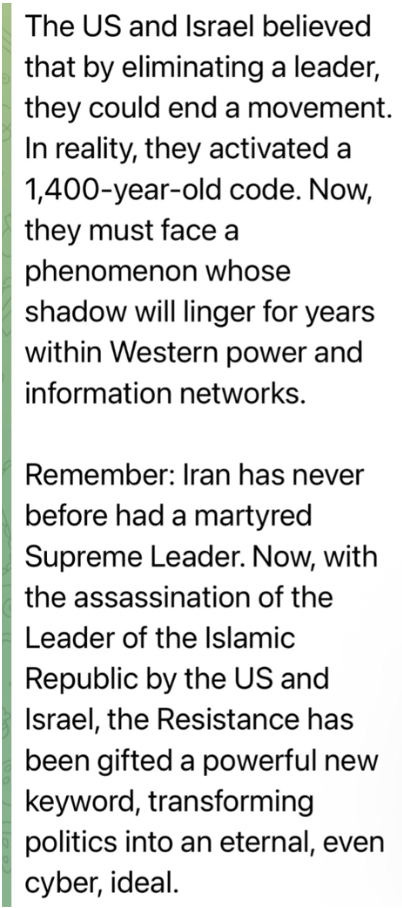
Image 4. Message on the Handala Hack official group on Telegram, claiming that the assassination of Iran’s Supreme Leader Khamenei will trigger a long cyber warfare campaign.
As of March 4th, the hacktivist group “Fatimiyoun Cyber Team” has claimed, via their official Telegram channel, responsibility for a large-scale attack targeting the official websites of Jordan’s government. On March 5th, the group “Islamic Cyber Resistance in Iraq – 313 Team”, also via their official channel, claimed the same type of large-scale attack against Bahrain’s government infrastructures. Other cyberattacks, carried out over multiple days and communicated through the official channels of the groups, targeted the governments of Qatar, Kuwait, and Israel.
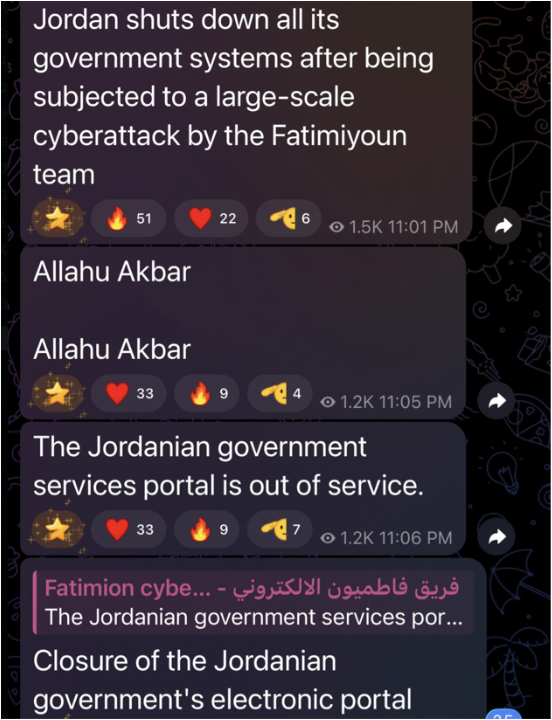
Image 5. Screenshot from the official “Fatimiyoun Cyber Team” group on Telegram, in which the group claims responsibility for the cyberattack on Jordanian government websites.
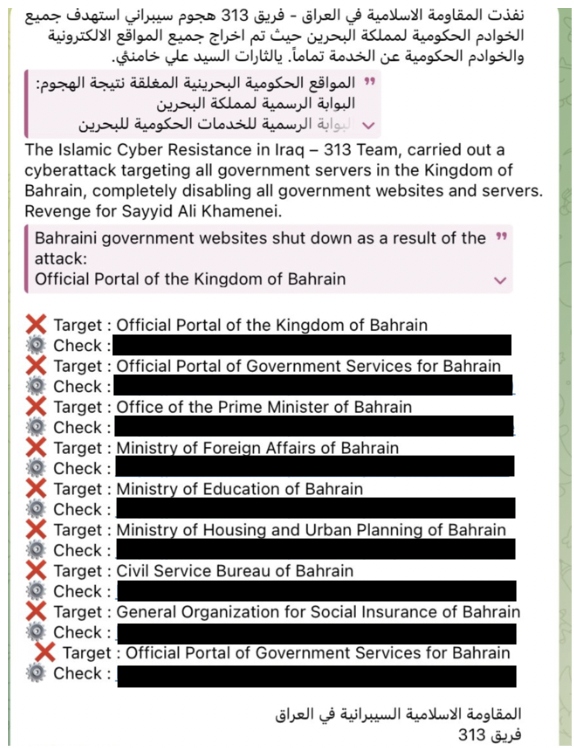
Image 6. Screenshot from the official “Islamic Cyber Resistance in Iraq – 313 Team” group on Telegram, claiming responsibility for the cyberattack against Bahrain.
This state-sponsored ecosystem gains additional momentum through religious authorisation that directly parallels CJM’s own jihadist framing. On 6 March 2026, IRGC-affiliated outlet Tasnim News amplified Ayatollah Nouri Hamedani’s fatwa – a religious ruling or opinion issued by Islamic mufti (legal scholar authorized to interpret Islamic law) -, declaring it “obligatory upon every Muslim, anywhere in the world, to avenge the blood of martyr Imam Khamenei” and that “anyone killed in this way will be considered a martyr”. This Shia religious edict, echoing multiple fatwas from senior clerics post-Epic Fury, creates a global call to action framing retaliation against US-Israeli strikes as a collective Muslim duty. While rooted in Twelver Shiism, the fatwa’s universal language (“every Muslim”) rhetorically flattens sectarian boundaries, establishing a permissive ideological environment where Sunni actors like CJM can position their “Global Cyber Jihad” as complementary rather than competing. For al-Qaeda affiliates, Iran’s cyber infrastructure thus becomes not just a tactical opportunity but a convergent operational space where shared anti-Western targeting aligns with overlapping religious mobilisation narratives – Sunni cyber jihadists answering a Shia call to arms through digital means.

Image 7. Screenshot from an IRGC-affiliated Telegram channel amplifying Ayatollah Nouri Hamedani’s jihad fatwa. Translation: “Ayatollah Nouri Hamedani’s Jihad Fatwa to Avenge the Blood of Martyr Imam Khamenei. It is obligatory upon every Muslim, anywhere in the world, to avenge the blood of martyr Imam Khamenei. The director of the office of Ayatollah Nouri Hamedani explained the details of this Shiite religious authority’s. Jihad Fatwa to avenge the blood of Imam Khamenei”.
For CJM, this combined technical-religious ecosystem offers clear tactical advantages. Iranian hacktivist networks maintain persistent access to compromised systems across multiple sectors, and the Electronic Operations Room facilitates the exchange of attack scripts and malware kits. By embedding within the broader pro-Iranian hacktivist surge, CJM activities blend into the noise of 149+ concurrent DDoS attacks. Therefore, attribution becomes functionally ambiguous, as the overlap in infrastructure, messaging channels, and tactics makes it difficult to determine whether a particular attack is directed by the IRGC, carried out independently by hacktivists, or opportunistically exploited by al-Qaeda-affiliated actors.
How AI Could Supercharge CJM-Style Recruitment And Its Connections To Hard Tech Trends
The CJM communiqué’s recruitment-focused language gains particular significance when viewed through the lens of AI’s expanding role in jihadist operations. Recent assessments highlight how groups like Islamic State Khorasan Province (ISKP or ISIS-K) have integrated AI into radicalisation strategies, using data-driven insights from social media behaviour to customise propaganda in real-time. ISKP now explicitly endorses AI use amongst recruiters: a notable ideological shift, as earlier jihadist movements questioned whether AI contradicted divine guidance.
For CJM’s stated objectives, emerging AI tools could provide operational enhancements that may amplify its collaboration with Iran. Large Language Models (LLMs) can parse open-source intelligence to identify vulnerable infrastructure and analyse security advisories for exploitable vulnerabilities. In environments where coordination structures, such as Iran’s Electronic Operations Room, are already present, such technologies could increase the speed at which information is collected, analysed, and translated into operational activity. At the same time, AI-driven systems are becoming more capable of analysing online engagement patterns and generating tailored content at scale. In extremist ecosystems, these capabilities could potentially be used to refine messaging strategies and more effectively target sympathetic audiences across digital platforms. CJM’s call for “believing men and women”, for instance, illustrates how future propaganda efforts might increasingly rely on adaptive or automated content to resonate with diverse online communities.
On the hard-tech side, CJM’s announcement crystallises a set of trends that have been reshaping the extremist threat landscape for several years. The first is the commodification of offensive capability. For instance, this could include commercial-off-the-shelf drones that violent non-state actors can buy cheaply online and convert into precision munitions, as well as cybercrime-as-a-service markets on the dark web that offer ready-made malware, DDoS capabilities, and supporting infrastructure accessible even to actors with limited technical expertise.
A second trend is the normalisation of function‑over‑ideology collaboration. In the physical space, al‑Qaeda and Islamic State factions have long been willing to share sourcing channels and design patterns for drones, IED components, and smuggling routes when it served their interests, even where doctrinal positions diverged. In the cyber domain, this dynamic is magnified because operational components are inherently modular: malware code, command-and-control infrastructures, botnets, and access credentials can be developed, traded, or reused independently of the political actors who created them. These technical building blocks can therefore circulate across online ecosystems and be repurposed by ideologically distinct groups without requiring deeper organisational alignment. CJM’s explicit willingness to “join Pro‑Iranian hacker movements” indicates that, at least in cyberspace, the Sunni-Shia divide is negotiable when shared tooling and target sets are on offer.
The third trend is the emergence of hybrid operating environments in which nation‑state, hacktivist, and terrorist actors cohabitate infrastructure and timelines. Iranian APT units, patriotic hacktivists, criminal crews moonlighting for the IRGC, and now CJM or similar jihadist formations can all operate within the same hosting providers, VPN endpoints, and anonymisation layers. They may even reuse identical command‑and‑control servers or web shells at different points in time. This creates what might be termed “attribution pollution”: technical indicators and attack patterns that could plausibly belong to any of several overlapping actors. From a defender’s perspective, this degrades the usefulness of labels such as “APT”, “hacktivist”, or “terrorist”, because the observable behaviour does not map cleanly to a single category, and it also benefits the attackers. Iran can deny responsibility for more aggressive activity by pointing to supposedly independent volunteers, while CJM can hide behind the more familiar spectre of Iranian state‑sponsored hacking.
Conclusion and Recommendations
These dynamics demand function-centred approaches over actor identity in both cyber defence and PCVE.
Tech platforms should weave toolchain mapping – the analytical process of identifying and tracing the sequence of tools, infrastructure, and techniques used by an attacker throughout a cyber operation, to reconstruct how the attack was conducted and identify links between campaigns or threat actors – directly into threat intelligence workflows. They can do so by using graph analytics to trace how malware variants, C2 domains, exploit kits, phishing frameworks, and even credential marketplaces flow between IRGC proxies, hacktivists, and emerging jihadist actors. CrowdStrike’s agentic threat intel shows this works in practice by autonomously surfacing interdependencies before CJM-style groups activate that infrastructure. The payoff comes through coordinated de-platforming across ecosystems: when one provider suspends a domain hosting Iranian ops room tools, allied platforms simultaneously block the jihadist Telegram channels redistributing them, transforming reactive moderation into predictive disruption that catches hybrid campaigns at formation rather than after they’ve blended into attribution noise.
To counter CJM recruitment in hacker subcultures, companies can partner with bug bounty platforms, CTF organisers, and coder communities for ethos-based PCVE campaigns that speak the language of technical problem-solving. The World Economic Forum’s 2026 Cybersecurity Outlook endorses this approach, where influencers – former blackhats turned whitehats – reframe scripting and pentesting skills as civic defence through defector narratives shared in various online forums and servers. HackerOne data show that structured bounty programs drive sustained hacker participation, with vulnerability disclosure programs yielding deeper engagement than open bounties, as hackers respond to clear incentives and community recognition. YesWeHack’s 2026 report reinforces this, finding 98% of pentesters prefer challenge formats that tie rewards to high-impact discoveries, suggesting similar mechanics could outcompete jihadist appeals by offering tangible career pathways.
Pre-emptive infrastructure kill switches offer another layer of defence, where hosting providers, Telegram administrators, VPN services, and even domain registrars trigger rapid takedowns on suspicious domains, channels, or endpoints showing hybrid signals. This includes Iranian ops room tooling cross-posted to jihadist groups, shared C2 servers lighting up across multiple branded campaigns, or VPN exit nodes suddenly handling traffic from both IRGC proxies and Sunni hacktivist claims. CrowdStrike’s agentic detection sets precise activation thresholds using real-time toolchain convergence, surgically excising bulletproof hosts and Telegram proxies without broad platform bans that drive users underground or fuel censorship narratives, forcing CJM coordination to restart from scratch while defenders maintain advantage through automated cross-provider coordination.
—
Daria Alexe is a Master of Science student in Intelligence and Security Studies at Liverpool John Moores University. She has previously worked as a geopolitical analyst and holds a Double Bachelor of Arts in Global Governance and Political Science, as well as a Master of Arts in Prevention of Armed Conflicts and Terrorism. Her work focuses on international security, terrorism, and CBRN threats, conducting intelligence and geopolitical analysis on extremist networks and illicit activities in high-risk contexts.
—
Are you a tech company interested in strengthening your capacity to counter terrorist and violent extremist activity online? Apply for GIFCT membership to join over 30 other tech platforms working together to prevent terrorists and violent extremists from exploiting online platforms by leveraging technology, expertise, and cross-sector partnerships.
