Modern conflict has been shaped by the use of new and emerging technologies. The use of drones is a prime example of a technology that has changed the nature of modern warfare. Drones have been adopted by both states and armed terrorist groups in almost every modern conflict theatre from Africa to the Middle East and parts of Asia. In the context of terrorism, the adoption of drones constitutes a tactical innovation by terrorist groups, shaped by intrinsic factors and extrinsic enablers that influence their innovation calculus.
This Insight examines the key factors shaping terrorist groups’ decisions to pursue particular technological innovations, with drone adoption as the primary case study. Examples from the Islamic State (IS) and Al-Qaeda (AQ), as well as other relevant groups, will be examined. Understanding a terrorist group’s innovation calculus is crucial for developing measures to stem the enablers that drive it, which could be useful to technology companies, security agencies and governments affected by them.
Defining Terrorist Innovation
Innovation can be defined as the development of a novel idea, tool or method. In the context of terrorism, terrorist groups rarely engage in a complete, novel invention of a new technology or methodology. In most cases, groups engage in novel forms of improvisation, adaptation, adoption or emulation of already existing techniques or methodologies to suit their own needs and objectives. Martha Crenshaw famously highlighted the three levels of terrorist innovation: strategic, organizational and tactical. The adoption of drones can be categorised as a tactical innovation, that is, a shift in a group’s operational execution and technology adoption.
Lubrano further highlights the differences between adaptation, emulation and improvisation and notes that the three represent “gateways to the innovation process, provided that they eventually go beyond the mere adoption of a new pattern or behaviour and result in the shattering and subsequent re-formulation of substantial aspects of the organisation’s modus operandi” [p. 250]. He notes that the key to innovation is the “redefinition of a behavioral pattern” [p. 253].
As the aim of this Insight is to understand the factors that determine a group’s decision to undertake a particular innovation, Adam Dolnik’s definition of terrorist innovation will be adopted. Dolnik defines terrorist innovation as the “act of introduction of a new method or technology or the improvement of an already existing capability” that “incorporates situations when a terrorist organization develops or discovers a new technology or tactic (radical/revolutionary innovation)” and “situations where it improves the use of a technology or tactic it already possesses (incremental/evolutionary innovation)” [p. 6]. At the level of the terrorist organisation, innovation should therefore be understood as the “adoption of a new tactic or technology” that it has not used or considered before [p. 6].
This aligns with Ackerman’s perspective that innovation need not comprise a single macro-invention but rather smaller enhancements that allow a weapon to cross a performance threshold [p.45]. However, as Paul Gill notes, for an innovation to occur, it must graduate from idea generation to full implementation [p. 575]. If a group lacks the capability to implement a creative concept, it falls short of innovation [p. 575].
Terrorist Innovation Model
Terrorist innovation is contingent upon intrinsic factors – factors internal and unique to a group – and extrinsic enablers – external catalysts that facilitate innovation and the adoption of technology. Both work in tandem to influence a terrorist group’s innovation calculus.
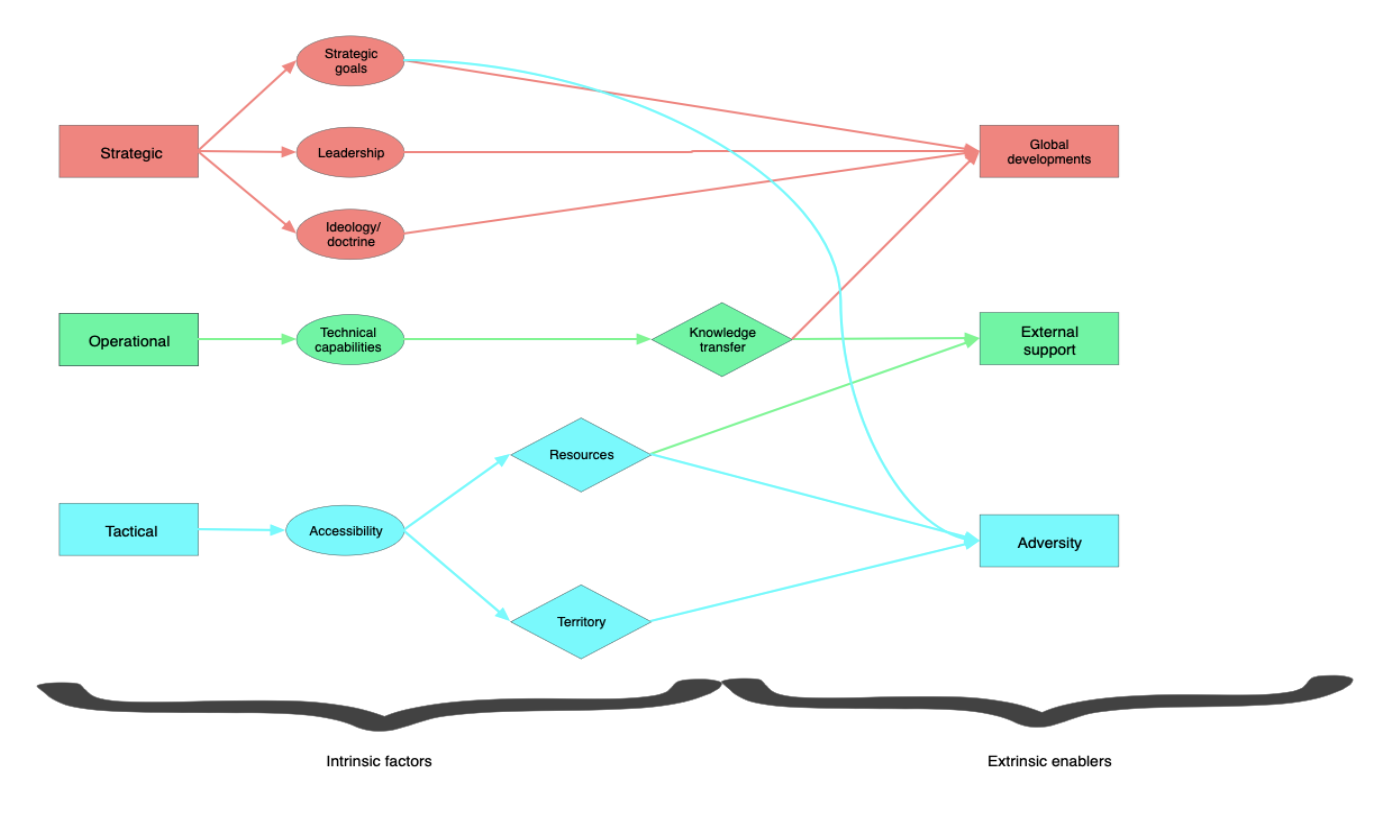
Figure 1: Terrorist Innovation Model (developed by the author).
Intrinsic factors
Strategic level
At the strategic level, three components play a key role in determining a group’s decision to innovate: strategic goals, leadership and ideology/doctrine. The use of a new technology is primarily motivated by a group’s strategic goals. These goals may encompass a group’s desire to gain an asymmetric advantage against a more powerful adversary, project a more powerful image, or circumvent logistical constraints or countermeasures.
IS developed a “centralized and bureaucratized” [p. 17] approach to drone manufacturing that allowed the group to exert control [p. 44] over the products of its program. The strategic goal behind the development, modification and adoption of drones was to provide the group with an asymmetric advantage against Coalition forces. IS leaders knew that they could not match the financial resources and capabilities of the United States and their other state partners. Drones provided a cheap, accessible avenue to fight back. IS began procuring [p.12] and using drones in 2014 for intelligence, surveillance and reconnaissance (ISR) missions and film propaganda videos, and then shifted to offensive use by 2016 [p. IV]. Drones were also heavily used by the group for propaganda videography, which boosted the group’s image and recruitment capacity.
Having leaders inclined toward developing a particular technology may shift a group’s decision-making calculus toward adopting or developing new technology. For example, Al-Qaeda in the Arabian Peninsula (AQAP) first adopted drones in mid-2023 under the direction of its former leader Khaled Batarfi, in an attempt to boost its image at a time of decline. Batarfi wanted to ensure the group’s survival. AQAP used commercial quadcopters to drop munitions on members of the Southern Transitional Council (STC) in Abyan and Shabwa. The drones were obtained with the assistance of Ansar Allah.
Doctrinal or religious justification for drone use has largely been absent, unlike the extensive theological debates surrounding weapons of mass destruction (WMD). This may reflect groups such as IS viewing drones as tools rather than tactics. Nevertheless, religious texts (such as Sura Al-Anfal) have been (mis)used in IS chatrooms to legitimise technological warfare and exhort supporters to employ any available means. Ideology or doctrine is often malleable enough to be tweaked to fit a group’s strategic goal, particularly when the technology has proven its worth and its utilitarian benefits.
Operational level
At the operational level, a group’s decision to innovate is contingent on its technical capabilities, with innovation occurring when intent and capacity align [p. 173]. Technical capabilities, in turn, are facilitated by knowledge transfer, which may be intrinsic or extrinsic depending on the type of transfer involved and external support (both explained below).
Several documents and reports suggest that IS invested significantly in the development of its drone capabilities. These included the formation of a specialised drone unit called the “Unmanned Aircraft of the Mujahideen” unit. This fell under the Al Bara’ bin Malik Brigade, a part of the aviation sector of the IS’ Committee for Military Manufacturing and Development. IS has also invested in recruiting specialist personnel with backgrounds in science and engineering to further develop these weapons.
Other jihadist groups, such as Hayat Tahrir Al-Sham (HTS), Al-Shabaab and AQAP have emulated IS in the development of their own drone capabilities. HTS developed its own drone unit, the Al-Shaheen brigade, which engaged in research, development, and drone operator training for over 10 years. The unit’s operations played a key role in HTS’ takeover of Damascus in 2024. Similarly, a July 2024 UN report suggested that Al-Shabaab is recruiting engineers to develop their drone and 3D-printing capabilities [p. 23]. AQAP was also found to have shown intent in developing its own in-house drone program with manufacturing capabilities [p. 15].
Tactical level
At the tactical level, accessibility to hardware, raw material and precursors is key. Accessibility is, in turn, governed by resources and territory. A group’s resource bank may be increased with external support, particularly by the state. Access to larger funds enables groups to invest in research, development and advanced hardware.
Territory provides a group with a safe haven to experiment and secure logistical supply routes for material and hardware. IS developed most of its chemical weapons and drone programs when it held territory [pp. 11-20]. They also had specialist factories that experimented with autonomous vehicle-borne improvised explosive devices (VBIEDs). IS is strategically exploited in Syria and Iraq to experiment and conduct drone operations, often with little opposition. The group’s possession of territory enabled it to take advantage of local facilities like universities, in the case of chemical weapons development, and establish complex procurement networks for drone parts. IS’ drone procurement network spanned across Europe, the Middle East and Asia, capitalising on front companies like the IBACS network and numerous commercial supply chains [p. 7].
The barriers to accessibility have been lowered by the commercial availability of dual-use technologies. Drones are commercially available in most countries, with little regulation surrounding their purchase. Additive manufacturing techniques such as 3D-printing are increasingly being used by terrorist groups to manufacture modifications and drone parts which they don’t have access to.
IS’ innovation pertaining to drones lies in its simplicity. Rassler notes that IS was able to creatively merge sophisticated commercial technology with low-tech components, and this “cobbling together of high- and low-tech systems” helped transform the commercial drones into “unique and fairly capable weapons” [p. IV]. This is being emulated by other groups such as IS affiliates in parts of Africa, AQAP, HTS, and Tehreek e-Taliban Pakistan (TTP).
Extrinsic enablers
Apart from intrinsic factors, several extrinsic enablers act as pull factors that drive innovation. The first is global technological developments. Terrorist groups often emulate tactics that have worked for other groups. Veilleux-Lepage and Rassler note that drone terrorism is punctuated by bursts of innovation (across the world) that groups normally emulate. Global developments also have the potential to influence a group’s strategic goals and its leadership’s thinking.
While it is unclear if IS tried to mimic a particular group or development, IS’ methods of improvisation have certainly been mimicked by other terrorist groups. The Kurdistan Workers Party (PKK), an avid employer of drone technology, was largely influenced by IS. Similarly, HTS’ use of suicide drones, drone swarms and the development of its own drone force largely mimicked IS in the Middle East. The adoption of drones by IS affiliates in Africa can also be linked back to IS in the Middle East. Developments in Russia and Ukraine have already been emulated by terror groups operating in other conflict theatres. For example, fiber optic drones, first introduced in the Russia-Ukraine conflict to circumvent counter-drone measures, have already made their way into the Sahel, with several terrorist groups there making use of them.
The second, and most important, factor is knowledge transfer, which bridges capabilities and the realisation of innovation. It occurs through intrinsic and extrinsic modes, including intra-group transfer within the organisation and its affiliates. For example, the Islamic State Sahel Province’s (ISSP) January 2026 attack on Dior Hamani International Airport in Niamey – reportedly involving drones for surveillance – was likely facilitated by support from ISWAP. Drone specialists from the Lake Chad basin were sent to the Sahel, mirroring IS Central’s late-2024 dispatch of 13 trainers from the Middle East to the Lake Chad basin to train ISWAP fighters in drone operations [p.8].
Inter-group transfers are transfers between groups with differing ideologies. An example of this is the nexus between Ansar Allah, AQAP and Al-Shabaab. Ansar Allah’s drone capabilities and access to advanced drones can be attributed to its affiliation with Iran. In this regard, external support, particularly by states, heavily influences a group’s capabilities and access to resources and advanced hardware.
Some of these weapons and expertise have leaked to Al-Shabaab, AQAP and even Islamic State Somalia (ISS), enhancing their drone capabilities. This has occurred despite Ansar Allah’s ideological differences with the rest, highlighting tacit and pragmatic cooperation among the groups. Similarly, increased collaboration and coordination between Al-Qaeda, the Afghan Taliban and TTP is likely to have facilitated the adoption of drones by the latter [p.17]. Apart from physical transfers, knowledge transfer increasingly occurs through intangible means, namely, social media.
The third extrinsic enabler is adversity. Adversity breeds innovation, and it can take several forms, the most common being a larger, more well-equipped adversary and logistical constraints. Drones offer groups an asymmetric advantage at a lower cost against government forces that are more superior. Logistical constraints, like shortages of weapons and specialist equipment, have also forced groups to innovate. IS tapped into the commercial drone market because they had a limited number of weapons options in their battles against Coalition forces. Evidence also suggests that they experimented with 3D-printing of munitions and drone parts as early as 2016, when a workshop was discovered. This may have been to circumvent shortages and logistical constraints. The strategic goals of a group may be influenced by the adversity it faces, forcing the leadership to take steps to circumvent them using innovation and technological adoption.
Implications for Counterterrorism
The use of new and emerging technologies by terrorist groups has elicited notable concern among counterterrorism agencies. Countermeasures against these technologies, like target hardening and developing hardware and control protocols, are essential. However, by understanding the determinants that govern a terrorist group’s innovation calculus, counterterrorism agencies may be better equipped to tailor their strategies to focus on upstream measures that emphasise a more strategic approach complemented by downstream, operational and tactical measures.
In this regard, targeting the intrinsic determinants of a group’s innovation and decision-making calculus – leadership, strategic goals, ideology, technical capabilities and accessibility – alongside the extrinsic enablers that facilitate innovation is crucial. While controlling global technological developments is nearly impossible, counterterrorism efforts must be focused on blocking logistical supply chains and routes, creating chokepoints for a group’s access to materials and resources, and most importantly, disrupting knowledge nodes and transfer mechanisms.
–
Rueben Dass is an Associate Research Fellow at the International Centre for Political Violence and Terrorism Research, a specialist unit of the S. Rajaratnam School of International Studies, Nanyang Technological University, Singapore and Fellow at the Conventional Arms and Ammunition Program at UNIDIR. He specialises in terrorist use of new technologies such as drones, 3D printing, and WMD.
–
Are you a tech company interested in strengthening your capacity to counter terrorist and violent extremist activity online? Apply for GIFCT membership to join over 30 other tech platforms working together to prevent terrorists and violent extremists from exploiting online platforms by leveraging technology, expertise, and cross-sector partnerships.
